@ddcaruso7 Ok, I have written a really simple web server program in Python that translates web requests into local keyboard presses. However, I must mention that you need to keep in mind that this server will be accessible by any device on your same WiFi network. So anyone who knows the URL can also send the same requests to your computer. You need to decide if you trust your own network.
Instructions:
- Download the program file (You may need to right click an select
Save As...) If you want to you can also view the code if you are interested in how it works: https://misc-scl-cdn.s3.amazonaws.com/FlicServer.py
- Place the program file in a folder on your Mac. For example
~/Documents/Flic or similar.
- Open Mac’s Terminal program and type
cd ~/Documents/Flic to move into the folder where you saved the program.
- Start the program by typing
python2.7 FlicServer.py
. If it starts successfully then it should write out “Started Flic Button server on port 4343” (The program can be terminated by pressing ctrl+c
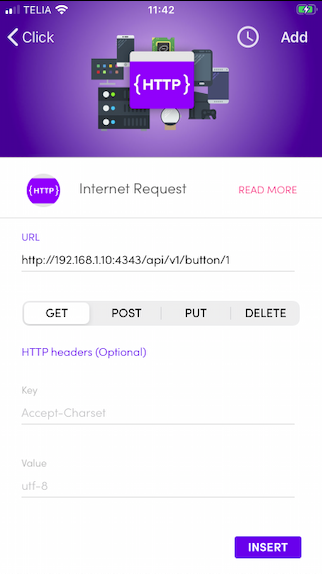
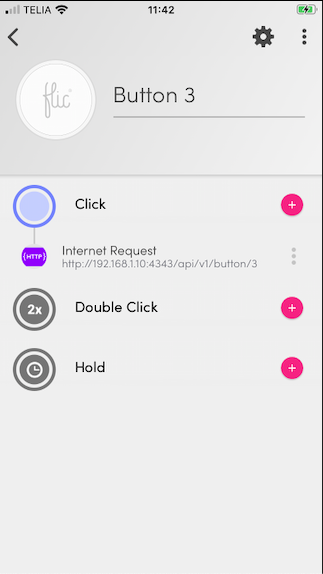
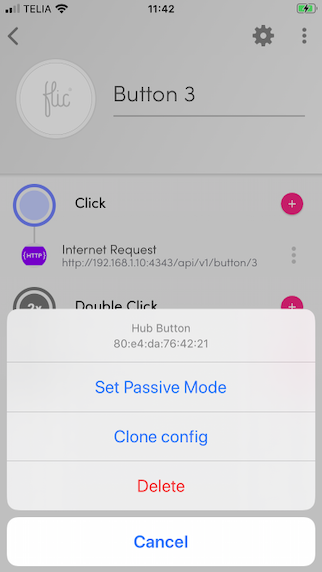
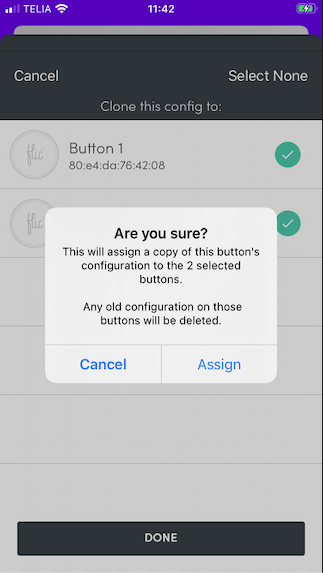
- The program is now running. To use it, you need to find the IP address of your Mac so that we can configure the Flic Hub to send the events correctly. Open System Preferences -> Network and make a note of the IP address (something similar to 192.168.1.10). The program will listen to requests on the URL:
http://192.168.1.10:4343/api/v1/button/1 (remember to change the IP address correctly). The last number "1" in the URL can be changed between 1-18 for the buttons.
Now, before we configure the Flics, we want to see if it actually works. So, open a text editor on your Mac and make sure that the window is selected. This way you will be able to see if the keyboard presses are working as they should. Using another computer/phone on your network, open a web browser and type the URL. If it works, then confirm the URL for all 18 buttons.
Let me know once you have gotten this far and I can help you with setting up the Flic Hub (if you don’t figure it out for yourself)
For reference, here is the code:
#!/usr/bin/python2.7
import sys
import time
import threading
from BaseHTTPServer import BaseHTTPRequestHandler, HTTPServer
from Quartz.CoreGraphics import CGEventPost
from Quartz.CoreGraphics import kCGHIDEventTap
from Quartz.CoreGraphics import CGEventCreateKeyboardEvent
# Button 1: '8' -> 28
# Button 2: '9' -> 25
# Button 3: 'b' -> 11
# Button 4: 'n' -> 45
# Button 5: 'm' -> 46
# Button 6: 'j' -> 38
# Button 7: 'k' -> 40
# Button 8: 'l' -> 37
# Button 9: 'z' -> 6
# Button 10: 'x' -> 7
# Button 11: 'c' -> 8
# Button 12: 'e' -> 14
# Button 13: 'r' -> 15
# Button 14: 'v' -> 9
# Button 15: 'q' -> 12
# Button 16: 'w' -> 13
# Button 17: '6' -> 22
# Button 18: '7' -> 26
PORT_NUMBER = 4343
def keyPress(keyCode):
print "Sending Keycode..."
eventDown = CGEventCreateKeyboardEvent(None, keyCode, True);
eventUp = CGEventCreateKeyboardEvent(None, keyCode, False);
CGEventPost(kCGHIDEventTap, eventDown);
CGEventPost(kCGHIDEventTap, eventUp);
class handleRoutes(BaseHTTPRequestHandler):
# GET request handler
def do_GET(self):
if (self.path.startswith('/api/v1/button/')):
keyCode = self.keyCodeForPath(self.path)
if (keyCode != None):
threading.Thread(target=keyPress, args=(keyCode,)).start()
return self.sendResponse('{"status": "success"}', 200, 'application/json')
else:
print "Could not find keycode for this button number."
return self.sendResponse('Not found.', 404, 'text/plain')
else:
return self.sendResponse('Not found.', 404, 'text/plain')
def sendResponse(self, res, status, type):
self.send_response(status)
self.send_header('Content-type', type)
self.end_headers()
self.wfile.write(res)
return
def keyCodeForPath(self, button):
if (button.endswith('/1')):
return 28
elif (button.endswith('/2')):
return 25
elif (button.endswith('/3')):
return 11
elif (button.endswith('/4')):
return 45
elif (button.endswith('/5')):
return 46
elif (button.endswith('/6')):
return 38
elif (button.endswith('/7')):
return 40
elif (button.endswith('/8')):
return 37
elif (button.endswith('/9')):
return 6
elif (button.endswith('/10')):
return 7
elif (button.endswith('/11')):
return 8
elif (button.endswith('/12')):
return 14
elif (button.endswith('/13')):
return 15
elif (button.endswith('/14')):
return 9
elif (button.endswith('/15')):
return 12
elif (button.endswith('/16')):
return 13
elif (button.endswith('/17')):
return 22
elif (button.endswith('/18')):
return 26
else:
return None
try:
server = HTTPServer(('', PORT_NUMBER), handleRoutes)
print 'Started Flic Button server on port ', PORT_NUMBER
server.serve_forever()
except KeyboardInterrupt:
print '\nClosing Flic Button server...'
server.socket.close()